MSc Cybersecurity — Robert Gordon University
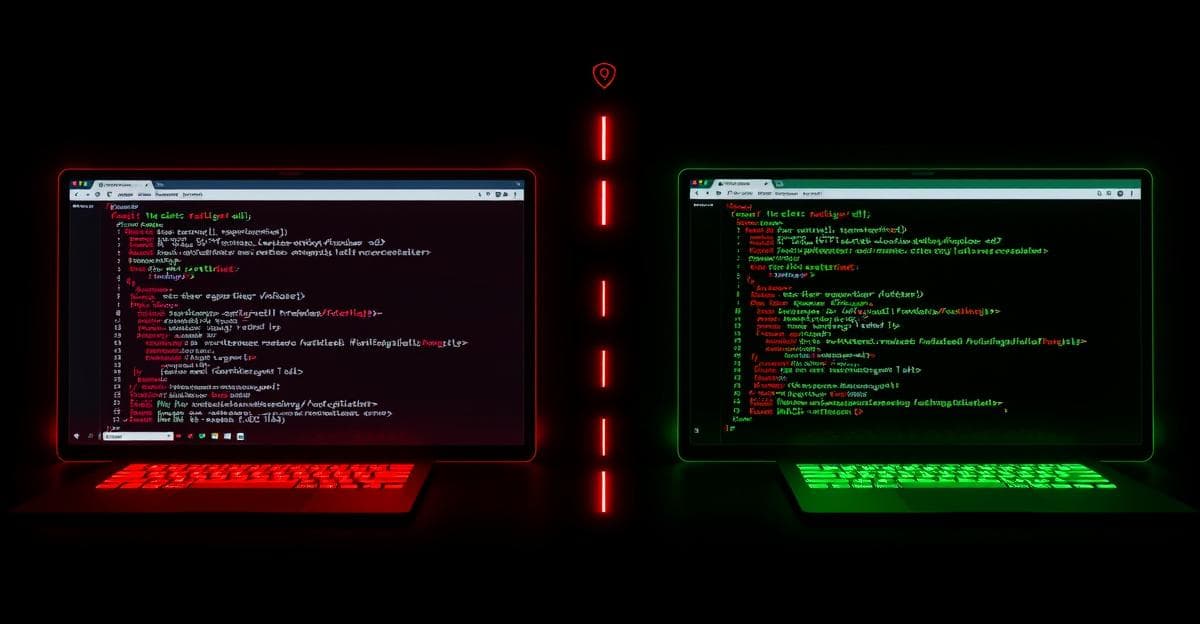
Web Application Penetration Testing & Hardening
Conducted a security assessment of a vulnerable web application, exploiting SQL injection, file upload bypass, XSS, and authentication weaknesses using Burp Suite and OWASP methodology. Implemented secure coding fixes and Apache server hardening.
Overview
This MSc project covered the full penetration testing cycle for a web application: reconnaissance, exploitation of identified vulnerabilities, documentation of findings, implementation of remediations, and verification that fixes held.
Scope
The target was a deliberately vulnerable web application (XAMPP environment) designed to exhibit common OWASP Top 10 vulnerabilities. The engagement simulated a black-box assessment where the tester begins with no knowledge of the application's internal structure.
Vulnerabilities Exploited
SQL Injection
- Identified unsanitised input fields accepting raw SQL
- Extracted database schema and user credentials via union-based SQLi
- Demonstrated authentication bypass using crafted SQL in the login form
File Upload Bypass
- Identified file upload functionality with client-side-only validation
- Bypassed MIME type checks to upload a web shell
- Demonstrated remote command execution via the uploaded shell
Cross-Site Scripting (XSS)
- Identified reflected XSS in search functionality
- Demonstrated session cookie theft via crafted payload
- Identified stored XSS in a user profile field persisting across sessions
Authentication Weaknesses
- Identified predictable session token generation
- Demonstrated session fixation vulnerability
- Identified lack of account lockout enabling brute-force attacks
Tools Used
- Burp Suite — primary proxy for request interception, modification, and repeater-based exploitation
- OWASP ZAP — supplementary scanning
- OWASP Testing Guide — methodology framework
- XAMPP — target application environment
Remediations Implemented
All identified vulnerabilities were remediated and verified:
- SQLi — parameterised queries implemented; input validation added at application boundary
- File upload — server-side MIME validation, file extension whitelist, and upload directory moved outside web root
- XSS — output encoding applied; Content Security Policy header configured
- Authentication — session tokens regenerated on login; account lockout policy implemented; secure cookie flags set
Apache Hardening Applied
- Server version disclosure disabled
- Directory listing disabled
- Unnecessary modules removed
- Security headers configured:
X-Frame-Options,X-Content-Type-Options,Referrer-Policy
Key Learnings
The OWASP Top 10 vulnerabilities are not theoretical — they appear consistently in real applications because they stem from common development patterns (trusting client input, building SQL queries with string concatenation, not encoding output). Understanding how to exploit them is inseparable from understanding how to prevent them. The remediation phase of a penetration test is where the real value for the organisation is produced.